Turn enterprise APIs into
governed agent tools
Agents get actions, not credentials.
KeyRunner lets AI agents call approved APIs with policy checks, isolated runtime credentials, and complete audit trails without exposing secrets.
KeyRunner converts enterprise APIs into governed AI tools through a six-step secure execution pipeline: API Catalog import via OpenAPI specs, Tool Registry conversion, Policy Check with RBAC enforcement, Credential Runtime secret injection from Vault or 1Password without exposing secrets to agents, downstream API Action execution, and immutable Audit Trail recording. Secrets are never exposed to AI agents. Runs entirely inside your infrastructure with no data exiting your network.
Runs inside your infrastructure·Secrets injected only at runtime
Agents call approved tools without ever receiving credentials.
Governed Execution Flow
See how KeyRunner works
From OpenAPI spec to governed agent tool in five steps. Credentials stay in your vault. PII never reaches the agent.
Import your API
Paste an OpenAPI spec. KeyRunner converts every endpoint into a named, governed tool — no changes to the downstream service.
Every layer of the execution stack, secured
From credential isolation to policy enforcement and audit trails, KeyRunner enforces security at each step so agents execute with capability, not credentials.
Start local. Ship confidently.
A local-first API client built for developer speed, with a security boundary that keeps secrets on your machine. No cloud dependency, no registration, no credential exposure.
No Signup or Login
Get started instantly without registration friction or account setup.
VS Code Extension & Desktop Apps
Use KeyRunner inside your editor or as a dedicated desktop app without changing your workflow.
Local Storage & Execution
Keep sensitive data on-device with local execution and a tighter security boundary.
Run Unlimited Collections
Test, organize, and execute as many collections as your workflow needs.
Mock Servers
Simulate APIs fast so development and testing can move before the backend is ready.
Scriptless Testing & Playground
Explore, chain, and validate requests without needing to write test scripts first.
More than processing a request
KeyRunner does not just forward traffic. It adds control, safety, and visibility around every API interaction.
Every request can be checked, filtered, and handled with stronger guardrails.
KeyRunner adds governance, observability, and runtime boundaries around each interaction.
It is not just request forwarding. It is request control with policy and context.
Why trust us?
KeyRunner is built to give security, platform, and developer teams a tighter execution model without slowing down daily work.
Security controls built into the workflow
KeyRunner is designed to protect execution paths, secrets, and tenant boundaries from the start.
Zero Trust Framework
Every request is authenticated and verified to reduce unauthorized access risk.
Encrypted Environment Variables
Sensitive configuration stays protected with stronger handling for runtime secrets.
Centralized KeyConnector
Enterprise requests can be routed through infrastructure that runs inside your environment.
Safer handling for sensitive information
KeyRunner reduces accidental exposure with controls focused on what developers actually send and receive.
Sensitive Data Redaction
PII, PHI, and PCI can be redacted according to tenant-defined security rules.
Secrets Scanner
Continuously scan collections and requests to identify risky values before they spread.
Data Anonymization
Anonymize response data when needed to preserve privacy and reduce downstream exposure.
Visibility for security and governance teams
Operational trust is not just about prevention. It also depends on auditability, monitoring, and evidence.
Compliance with Industry Standards
Practices align with major compliance expectations so organizations can move with more confidence.
Audit Trails
Keep detailed records of actions and system behavior for accountability and review.
User Activity Monitoring
Track behavior across the platform to surface operational patterns and potential concerns.
Built for security teams, trusted by developers
Every control in KeyRunner is designed to reduce credential exposure, enforce policy at runtime, and give compliance teams the audit trail they need.
Secure API workflows for humans and AI.
Build, test, monitor, and collaborate on APIs from a local-first workspace.
When agents need access, expose approved APIs as safe AI tools through KeyRunner.
- API client
- Collections
- Environments
- Mock servers
- Scriptless testing
- Local secrets
- Basic secret scanner
- Desktop, VS Code, and CLI
No credit card required
- Team workspaces
- Monitoring
- SSO
- RBAC
- Audit logs
- 90-day audit retention
- Secret isolation
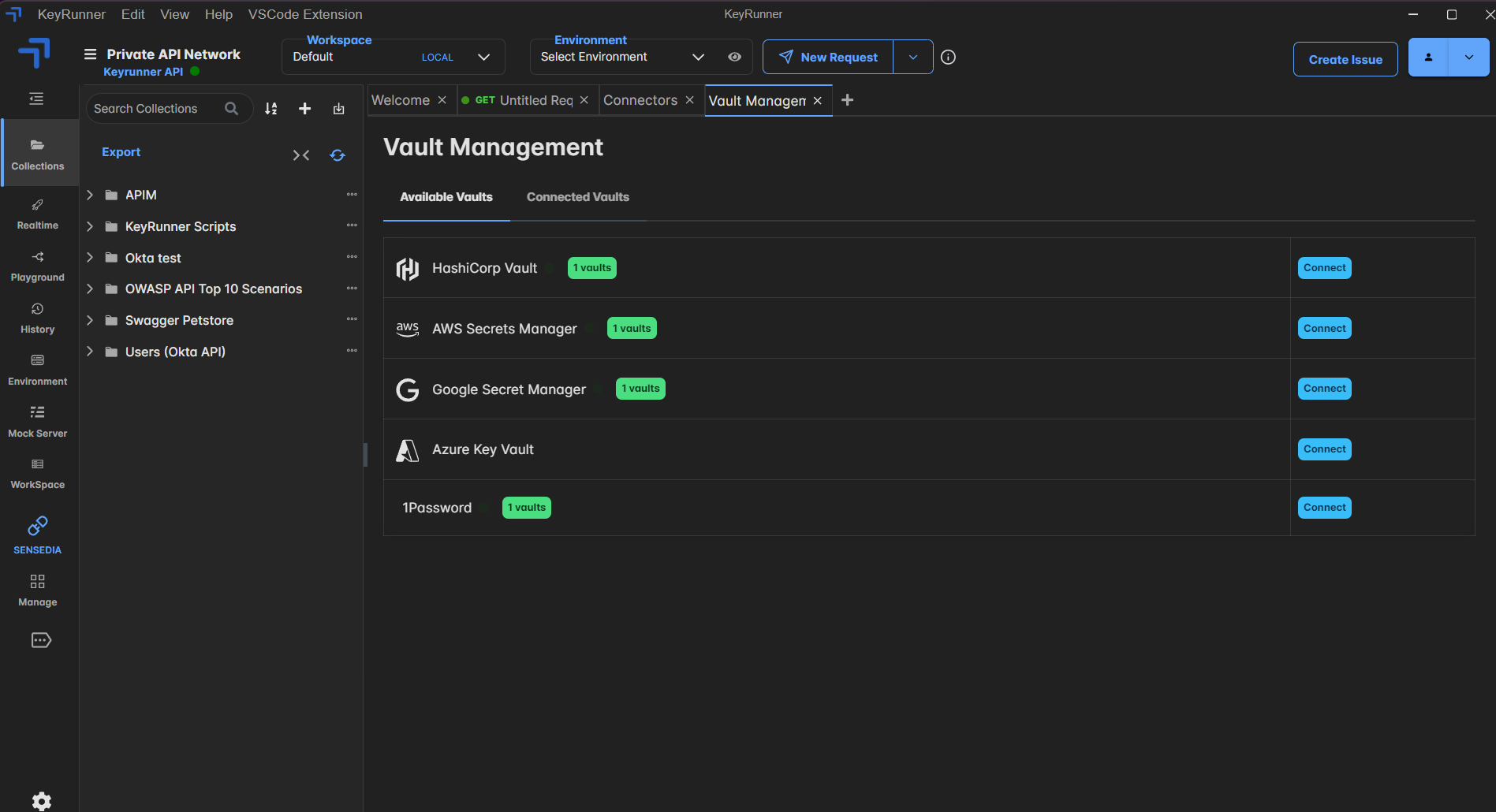
- Secret store integration
- Sensitive data redaction
- Scheduled testing
- CI/CD integration
- Slack + GitHub support
- Team collaboration
We get your team set up within 24 hrs
- Convert APIs into AI tools
- Expose tools through KeyRunner MCP
- No raw API keys to agents
- Policy before execution
- Runtime secret resolution
- Sensitive response redaction
- Audit record for every tool call
- Runs inside your environment
Add to any Explorer workspace
- Extended audit retention
- Advanced compliance controls
- SIEM integration
- Custom data residency
- Private deployment options
- Dedicated support & SLA
- Volume discounts
Give agents capability. Not credentials.
Start with the free API client for developers. Add policy enforcement, credential isolation, and audit trails when your agentic workflows need enterprise-grade governance.
Credentials are injected at runtime, inside your infrastructure. Agents invoke named actions, nothing more.
