The execution layer forsecure enterprise agents.
KeyRunner turns internal APIs into governed agent tools — runtime control, secret isolation, and full auditability. Built for security teams deploying AI in regulated environments.
What happens when agents access enterprise systems without control.
Most AI integrations wire agents directly to APIs. That works in a demo but it creates serious exposure in production.
Agents issued raw API keys can leak credentials in prompts, logs, or model outputs.
Without a governed surface, agents can invoke any endpoint not just the approved ones.
Most direct integrations produce zero structured record of what the agent actually did.
Regulated industries require demonstrable controls on automated actions. Ad-hoc integrations fail audit.
One governed layer between agent and enterprise.
KeyRunner sits between the AI agent and your internal systems, controlling every interaction from tool call to audit record.
Six stages. Every execution. No exceptions.
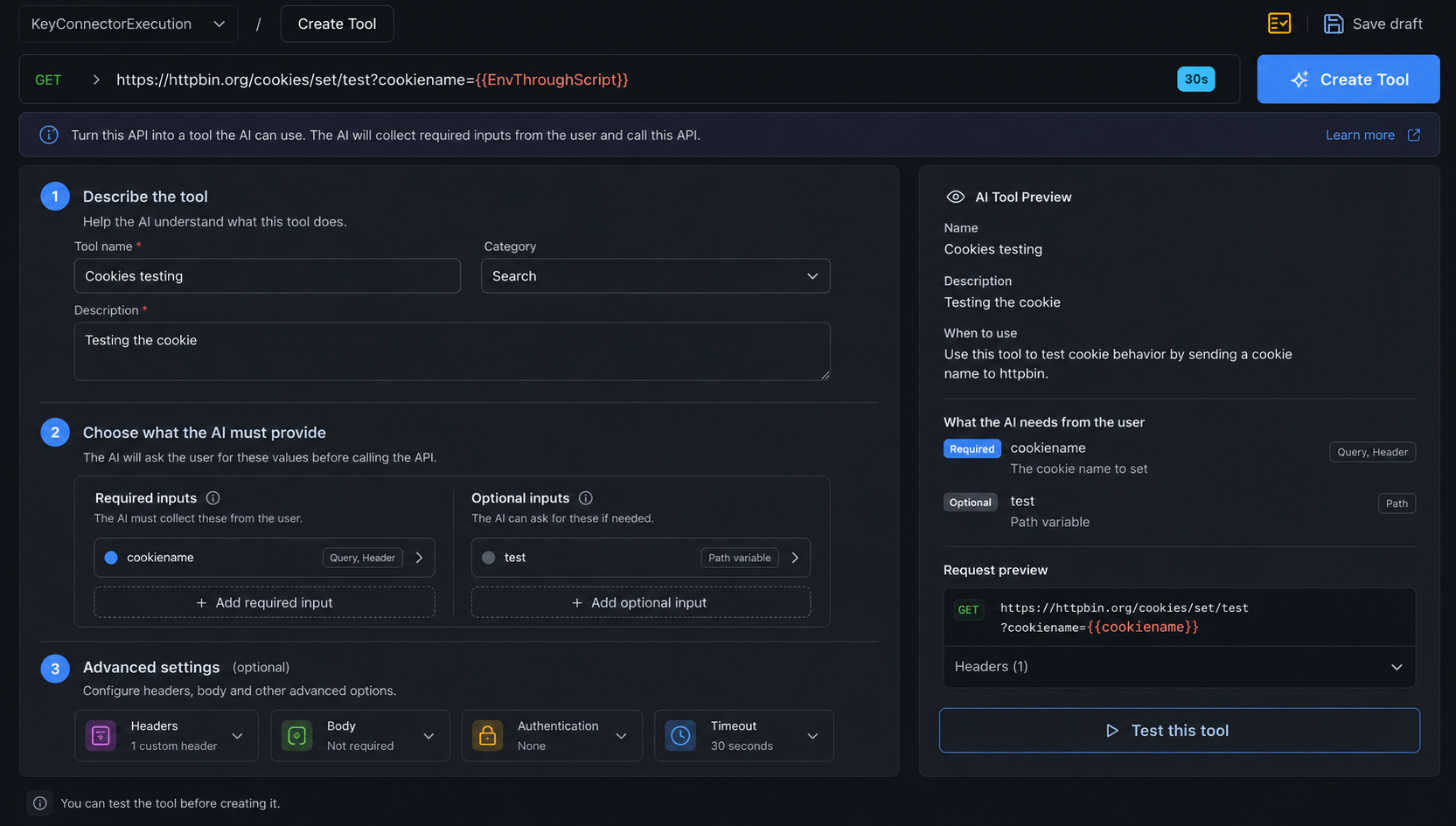
Every agent tool call passes through a defined pipeline inside your infrastructure boundary before any enterprise system is touched.
Verify agent identity and confirm the tool is on the approved surface.
Enforce rate limits, scope boundaries, and business rules.
Pull credentials from vault — injected at execution time, never passed to agent.
Make the governed API call inside your infrastructure boundary.
Strip sensitive fields before the response reaches the model.
Write a structured log including policy decisions, timing, and redaction status.
The difference at the execution layer.
Everything a security team needs to ship agents into production.
KeyRunner is built for the constraints of enterprise environments — not retrofitted for them.
Role-based tool access
Define exactly which agents access which tools, with scope limits and per-agent policies enforced at runtime.
Vault-native credential injection
HashiCorp Vault, AWS Secrets Manager, or Azure Key Vault. Credentials are never passed to agents.
OpenTelemetry-compatible telemetry
Every tool execution produces spans compatible with Datadog, Splunk, or your SIEM of choice.
Policy-as-code enforcement
Version-controlled execution policies, deployed independently of agent logic and testable in CI.
No external control plane
The execution layer runs entirely within your infrastructure. No data leaves your boundary to a KeyRunner SaaS.
Per-tool circuit breakers
Automatically halt tool execution on anomalous patterns. Configurable thresholds per tool, per agent, per environment.
{
"executionId": "exec_01JSDK8Q7A9F",
"tool": "create_ticket",
"agentId": "agent_support_v2",
"policyDecision": "allow",
"appliedPolicies": [
"rate_limit_ok",
"scope_matched"
],
"secretsResolved": ["JIRA_API_KEY"],
"status": "success",
"redactionApplied": true,
"durationMs": 142,
"timestamp": "2025-03-14T10:22:11Z"
}A complete execution record on every run.
Every tool call produces a structured record: what ran, which agent ran it, which policies applied, whether secrets were resolved, and whether redaction occurred.
Execution IDs for complete traceability
Policy decisions captured on every call
Secret resolution logged without exposing values
Redaction status and duration recorded
Feed directly into SIEM, Splunk, or Datadog
Built for regulated industries from the start.
Audit evidence, execution records, and compliance documentation are first-class outputs — not afterthoughts.

Annual third-party audit of security controls across availability, confidentiality, and processing integrity.

Data handling and access controls aligned to EU regulatory requirements for enterprise deployments.

Controls supporting healthcare data handling requirements in automated agent workflows.
Governed tools for the agent.Enterprise control for your business.
Talk to our team about how KeyRunner fits your agent deployment, security requirements, and compliance posture.
